The average cost of a data breach in the United States is $9.44 million! It’s no wonder why businesses and individuals alike are so concerned about protecting confidential data.
And one of the most popular ways to secure digital communication is pretty good privacy (PGP) encryption, a form of end-to-end encryption.
So in this post, we will discuss what PGP encryption is, how it works, and why it’s important.
We’ll also look at some examples of how PGP can be used in everyday life to protect your data.
Let’s begin!
Understanding PGP Encryption
Encryption is a term we have all come across. It’s the process of scrambling information so that it can be decoded only by people who have access to the encryption key.
And PGP is a type of encryption that was originally developed in 1991 by Phil Zimmermann as a means of protecting online communication from any third-party eavesdroppers.
Any information sent with PGP is converted into unreadable ciphertext before being transmitted, with only the intended recipient being able to decrypt it using a key.
PGP also provides authentication, allowing users to verify the sender and detect any tampering that could have happened during transmission.
Now that you have a general understanding of PGP, let’s dive deeper into how it works.
How PGP Encryption Works
What’s unique about PGP encryption is that it uses both an asymmetric-key algorithm and a symmetric-key algorithm to encrypt your data.
Asymmetric-Key Algorithm
The asymmetric-key algorithm uses two different keys — one to encrypt the data, and one to decrypt it. This is known as public-key cryptography, and it’s the same system used for digital signatures.
The sender encrypts the data with the recipient’s public key (which is known to everyone), and only the holder of the corresponding private key (which only the recipient knows) can decrypt it.
Symmetric-Key Algorithm
The symmetric-key algorithm is another way to encrypt data. This method uses a single key for both encryption and decryption, which must be shared between the sender and the recipient. In other words, if I were to send you an email and encrypt it using a symmetric-key algorithm, I would need to give you the key so you could read it.
The Combination
Here’s how the encryption process looks like when PGP uses both of these methods in conjunction:
1. Joseph wants to send a secure message to Sarah.
2. He uses PGP, which starts by generating a unique session key for the data he is sending. This session key is generated using the symmetric algorithm.
3. PGP uses this session key to encrypt Joseph’s message.
4. Next, Joseph’s session key is itself encrypted using Sarah’s public key. This ensures that only Sarah can read it, as she is the only person with the corresponding private key.
5. Finally, both the encrypted message and the encrypted session key is sent to Sarah.
6. On the other end, Sarah uses her private key to decrypt the session key.
7. The decrypted session key is then used to decrypt the message.
And there you have it — a secure communication achieved with PGP encryption!
Benefits And Limitations Of PGP Encryption
As with any method of encryption, there are both benefits and limitations to using PGP. Let’s take a look at some of them now.
Benefits Of PGP Encryption
The biggest benefit of PGP encryption is that it’s highly secure. The use of both symmetric and asymmetric encryption algorithms makes it nearly impossible to crack.
PGP also offers authentication features, which help users verify each other’s identities prior to exchanging data. This helps guard against Man-in-the-Middle (MITM) attacks and other forms of tampering, which are surprisingly prevalent. A study reveals that around 35% of all exploitation activities involve MITM attacks.
Another pro of using PGP is its speed. To encrypt and decrypt emails or files with the public key would be extremely time consuming and require a large amount of computing power.
PGP solves this issue by using public-key cryptography only to encrypt the session key, which is significantly faster and requires less computing power than symmetric cryptography for entire messages.
Limitations Of PGP Encryption
One of the biggest drawbacks of PGP encryption is its complexity. The process is quite complicated and requires a good understanding of cryptography to use effectively.
Secondly, PGP is only as strong as the key used for encryption. If a weak key is employed, then it won’t be secure and can easily be cracked by a determined hacker.
Also, if you misplace your private key or forget the passphrase, you won’t be able to access any data that was encrypted with it.
Real-World Applications Of PGP Encryption
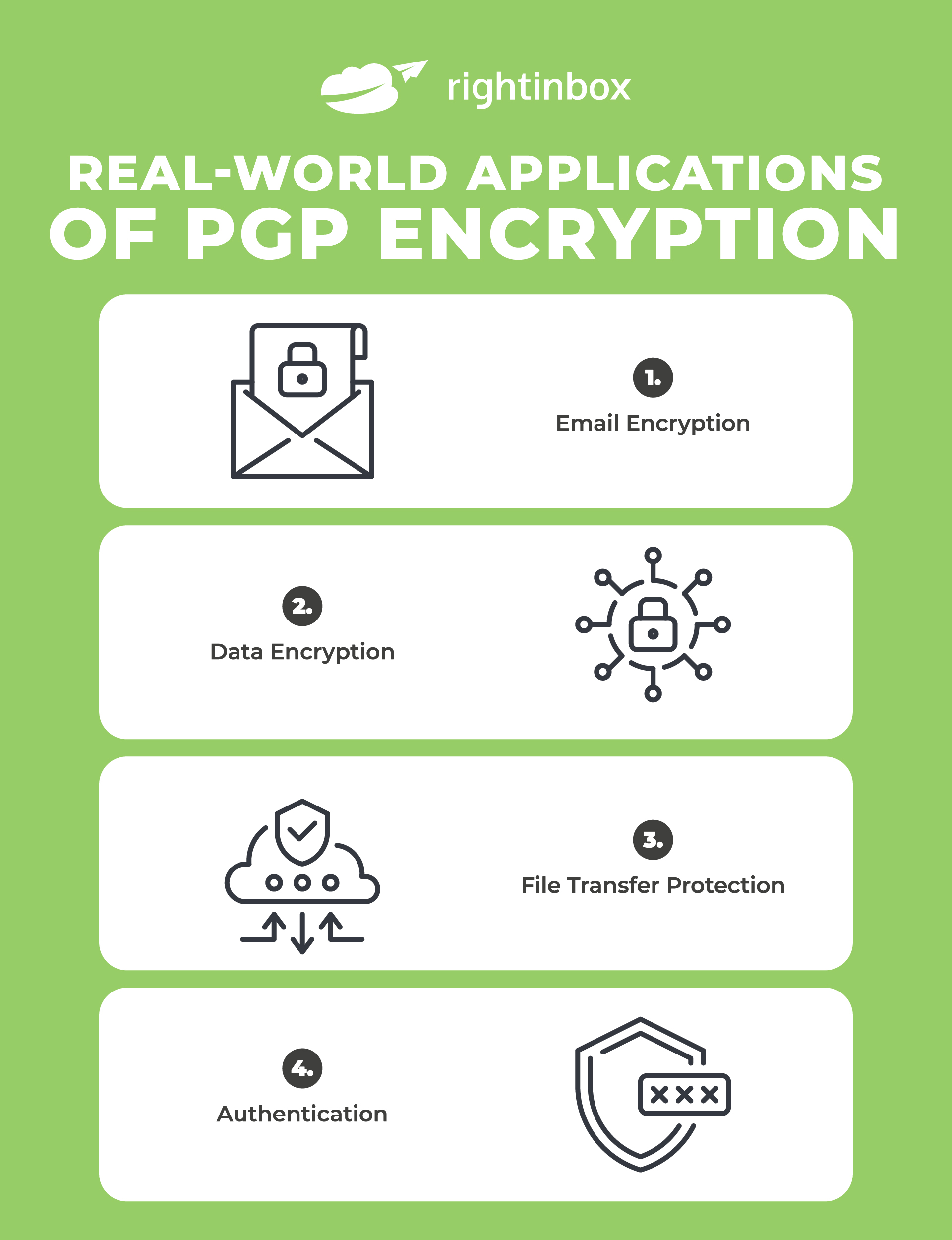
PGP encryption is used in many real-world situations, ranging from securing emails to protecting user data. Here are four examples of how it’s being employed in today’s world:
- Email Encryption – PGP can be used to send encrypted emails between two parties, ensuring that only the intended recipient can read them. It’s often used by corporate entities and organizations to protect sensitive data from falling into the wrong hands.
- Data Encryption – Companies often use PGP encryption to secure confidential customer data and other sensitive information. This ensures that only authorized personnel can access the encrypted files and user privacy remains protected.
- File Transfer Protection – When transferring large amounts of data over the internet, it’s important to ensure that the files remain secure and unaltered. PGP can be used to encrypt files during transfer, protecting them against malicious actors or data breaches.
- Authentication – One of the primary functions of PGP is providing authentication between two parties, allowing them to verify each other’s identities before exchanging data. This is often used in financial transactions, ensuring that both parties are who they say they are.
Final Words
So there you have it — a detailed explanation of what PGP encryption is and how it works.
If you’re still confused, just remember that it’s a way to scramble data so that the wrong people can’t make sense of it. And in doing so, PGP encryption uses both a public and private key to make things super-secure.
Track emails, email reminders & templates in Gmail for free
Upgrade Gmail with the features it’s missing
Add to GmailDavid Campbell
David Campbell is the editor of the Right Inbox blog. He is passionate about email productivity and getting more done in less time.